Resources
Browse our resource library to watch past webinars or download guides that help you stay secure and/or productive.

Entra ID Identity Attack Readiness Pack | Conditional Access Checklist
Enhance your Entra ID security with practical tools and strategies to mitigate identity risks and communicate effectively with senior ...
DownloadFilter by
Cybersecurity
Cloud
Entra ID Identity Attack Readiness Pack | Conditional Access Checklist
Enhance your Entra ID security with practical tools and strategies to mitigate identity risks and communicate effectively with senior leadership.
Download
Azure Landing Zone Readiness Template
Ensure your Azure landing zone is production-ready with our checklist for deploying secure workloads in a governed environment. Download the template now.
Download
Cloud Workload Placement Workshop Pack
Make informed decisions between Azure and private cloud with our structured workshop, designed for IT leaders to assess workloads based on requirements and business ...
Download
M365 AI Phishing And BEC Defence Kit
Enhance your defenses against modern phishing and BEC scams with the Microsoft 365 AI Phishing and Defence Kit. Access actionable resources to protect your organisation ...
Download
Shadow IT Audit Checklist
Download our Shadow IT checklist to identify unapproved tools and manage risks effectively without blaming employees.
Download
Cybersecurity in Microsoft 365 – Lessons from the Frontline Webinar
Join our free webinar to learn how to strengthen your Microsoft 365 cyber security defenses with insights from experts and a live cyber attack simulation.
Watch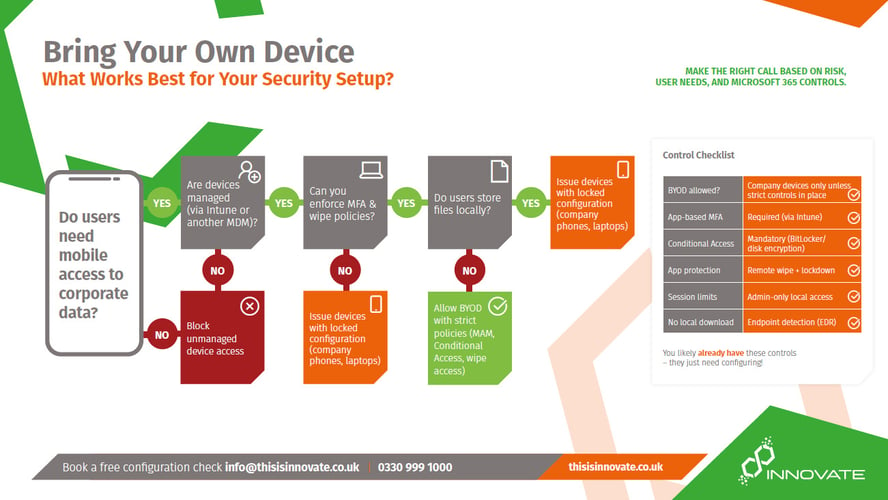
BYOD Risks and Security Measures PDF
Explore the risks and best practices of BYOD policies. Use our decision tree and expert guide to secure remote work and protect corporate data effectively.
Download
Backup, Replication, Redundancy and Recovery Best Practices Infographic
Ensure your data's safety with proactive strategies for M365. Download our guide to strengthen your cybersecurity and stay prepared against power cuts and cyber threats.
Download
Microsoft 365 Security Assessment Checklist
Identify vulnerabilities and strengthen your defenses with our free checklist.
Download
Cybersecurity in Microsoft 365 Slide Deck
Explore essential cybersecurity strategies for Microsoft 365, featuring insights on ransomware, security trends, and Microsoft's Defender XDR offerings to enhance ...
Download
Conditional Access Guide
Download our quick guide to conditional access policies - what it is, what it's capable of and how to use it.
Download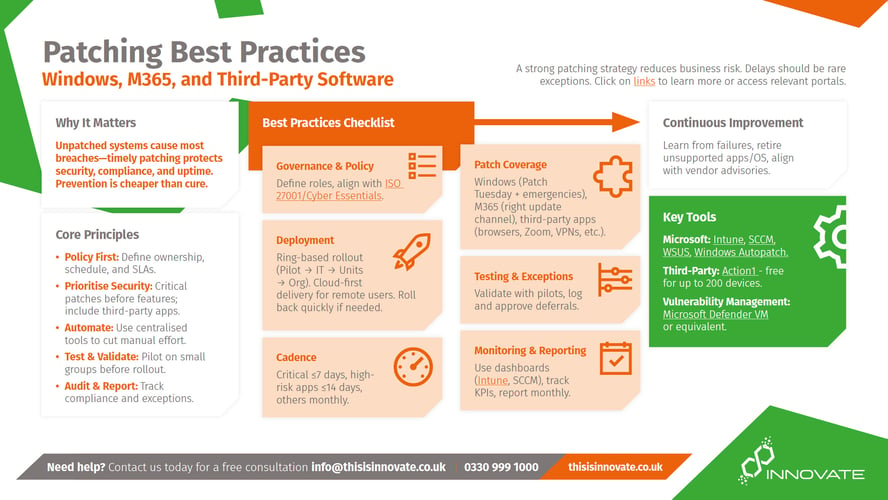
Patching Best Practices PDF
Stay secure by mastering patching with our guide. Discover best practices and access our favourite free patching tool for efficient software updates.
Download
M365 Cybersecurity 101 Employee Guide
An easy-to-understand guide to share with your staff to keep themselves safe with Microsoft 365
Download
M365 Security Aspects Guide
Secure your Microsoft 365 environment with our essential guide, featuring best practices for Multi-Factor Authentication and Zero Trust policies to enhance your ...
Download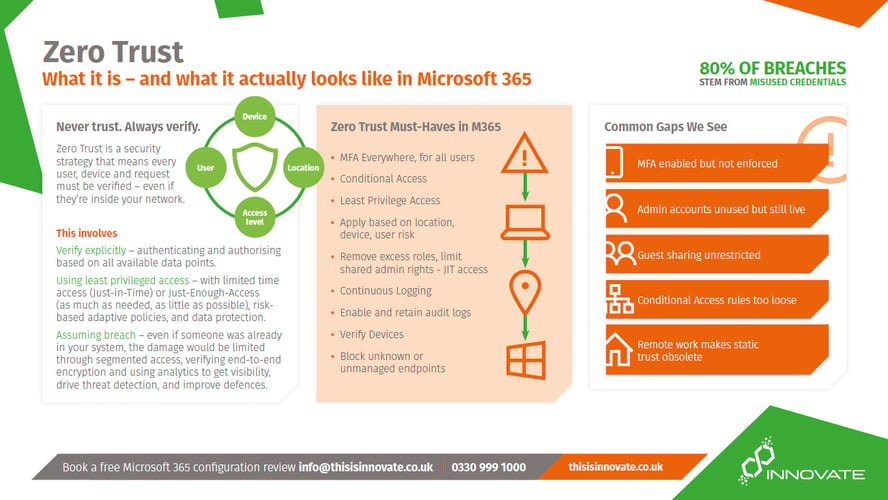
Zero Trust Info Sheet
Download this info sheet to learn more about Zero Trust and how to implement it in your organisation.
Download
MSP Microsoft 365 Security Checklist
Evaluate your IT support's effectiveness with our checklist. Download now to assess your cybersecurity posture in M365 and ensure they are meeting your needs.
Download
M365 Cybersecurity 101 Employer Guide
An at-a-glance guide at settings within M365 to strengthen your security posture beyond default settings.
Download